11.May.2021
Information security
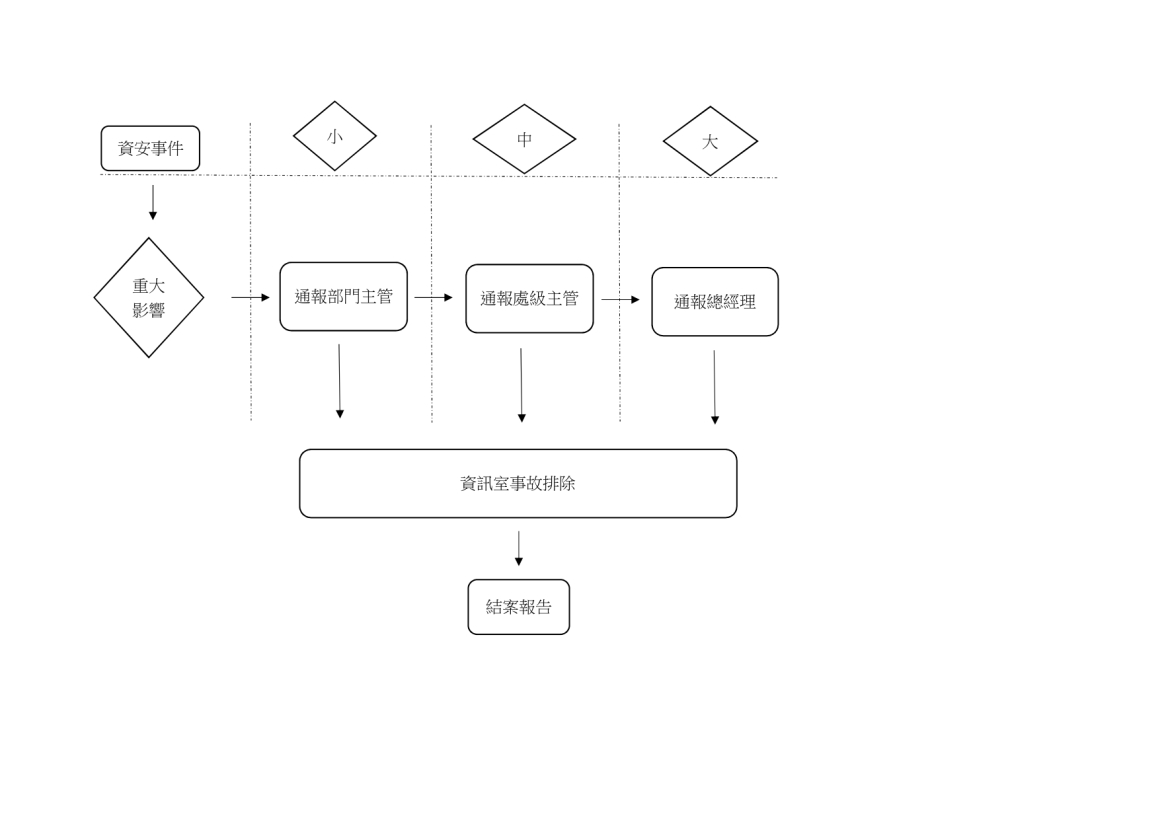
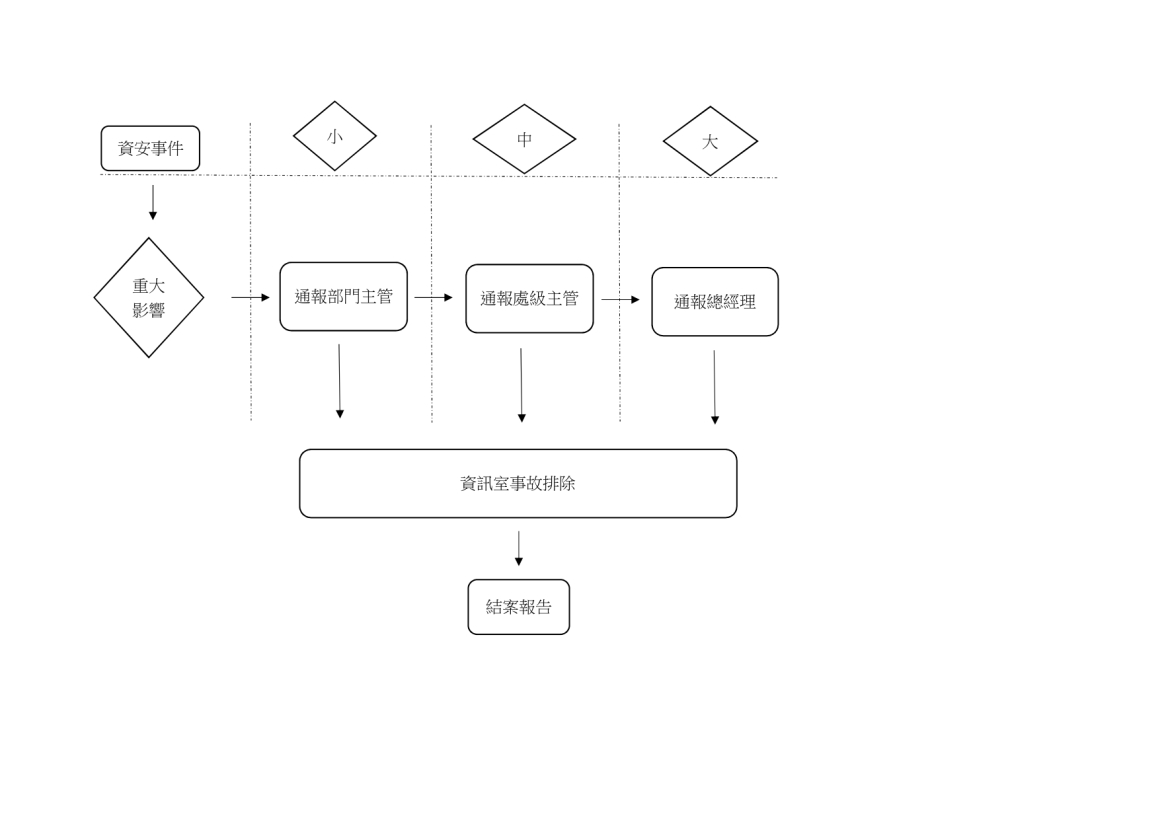
1. Information security policy and promotion organization
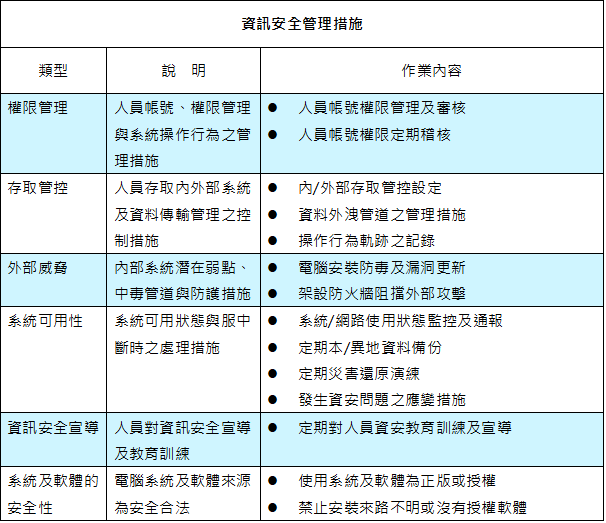
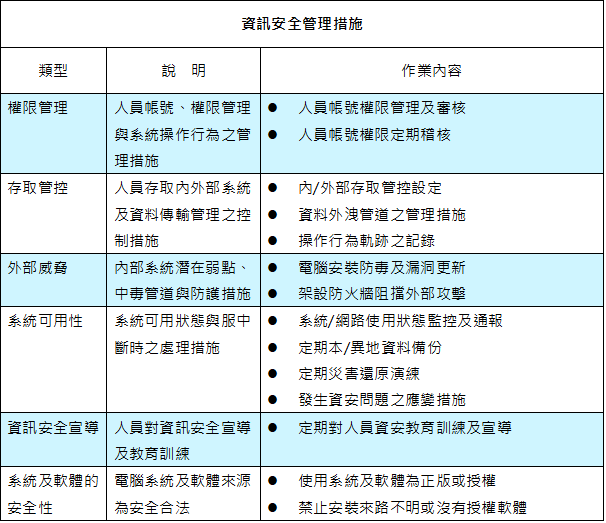
4. The information security management measures implemented by our company include the following
5. Continuous improvement of information security and performance management mechanism
- The responsible unit for information security of the company is the information room (including 1 dedicated information security manager and 1 dedicated information security staff member), which is responsible for planning, executing and promoting information security management matters, and promoting information security awareness.
- The company's personnel who use information systems must receive information security promotion at least once a year. In addition, supervisors and personnel responsible for information security must receive information security professional course training at least once a year.
- Ensure the data security of core business, the integrity of services and data, and the continuous operation of services.
- Implement management methods and standard operating procedures for user platform development and maintenance, computer room management, and outsourcing management.
- The information security landscape and scope should respond to the requirements and maintenance of the company's important business processes.
- Regularly implement education and publicity on information security matters to promote colleagues’ information security concepts and strengthen their awareness of related information security responsibilities.
- Employees work in accordance with various management regulations and operating procedures to maintain the normal operation of the company.
- The execution of information business activities must comply with the requirements of relevant laws or regulations.
- Implement regular monitoring and information security internal audit systems to ensure that information security management is implemented in daily maintenance operations and business activities.
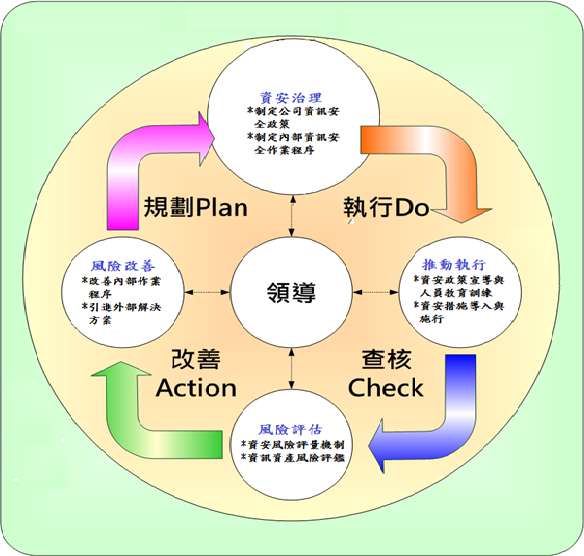
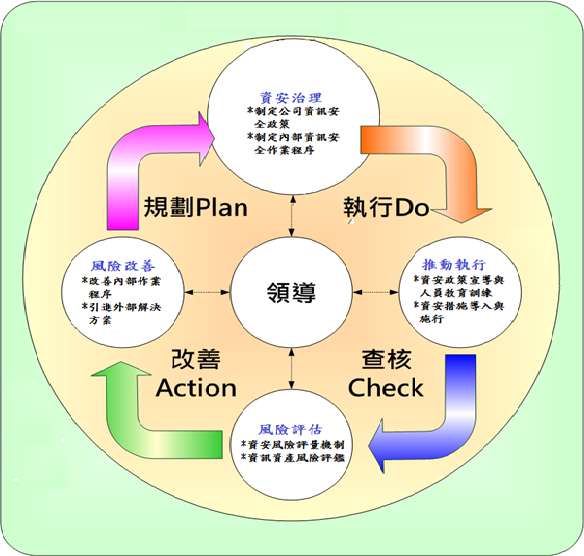
- Organizational operation model - adopt PDCA (Plan-Do-Check-Act) cycle management to ensure the achievement of reliability goals and continuous improvement.
4. The information security management measures implemented by our company include the following
5. Continuous improvement of information security and performance management mechanism
- Regularly report the implementation status of information security to the general manager to ensure the appropriateness and effectiveness of operations.
- Regularly conduct internal information security audits, formulate improvement measures for discovered matters, and regularly track improvements.